Implementing AWS Single Sign On (SSO) using Google Workspace (formerly G Suite)

If your organization useing Google Workspace (formerly G Suite) and AWS then you can connect AWS SSO to Google Workspace (G Suite) allowing your users to access AWS accounts with their Google Workspace (G Suite) credentials.
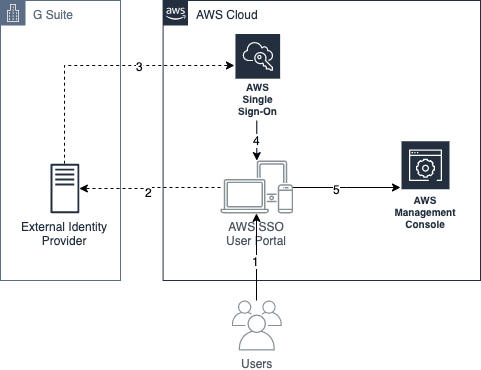
How it works
When you will use Google Workspace (G Suite) to authenticate and manage your users, you will have to create a user in your AWS SSO. The user entity will not be a user account, but it will be a logical object. Which maps a Google Workspace (G Suite) user via its primary email address as the username to the user acccount in AWS SSO. The user entity in AWS SSO allows you to grant a Google Workspace (G Suite) user access to AWS accounts and define its permissions in those accounts.
Prerequisites
You need to be a
super administrator privilegesinGoogle Workspace (G Suite)and need to have access to the Google Admin console.You need to have setup
AWS OrganizationswithAll features set to enabled. If not setup yet please follw this (How to setup AWS Organizations)You need to have management (root) account access of the Organizations with administrator privileges.
setup an external identity provider in AWS SSO
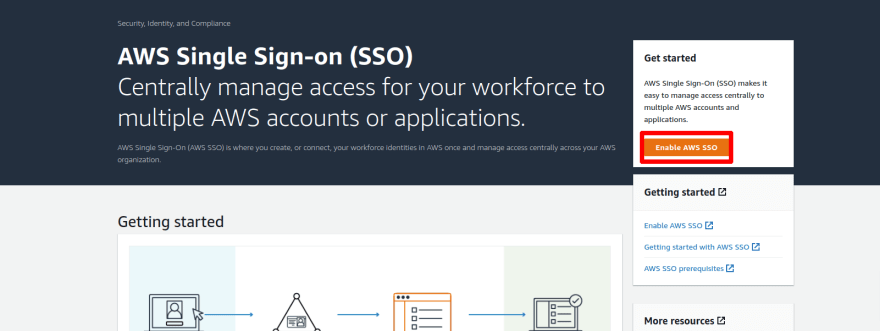
- Login to your Organizations management account and open
AWS Signle Sign-On (SSO)service.
- You will see
You seccessfully enabled AWS SSOmessage. SelectChoose your identity source.
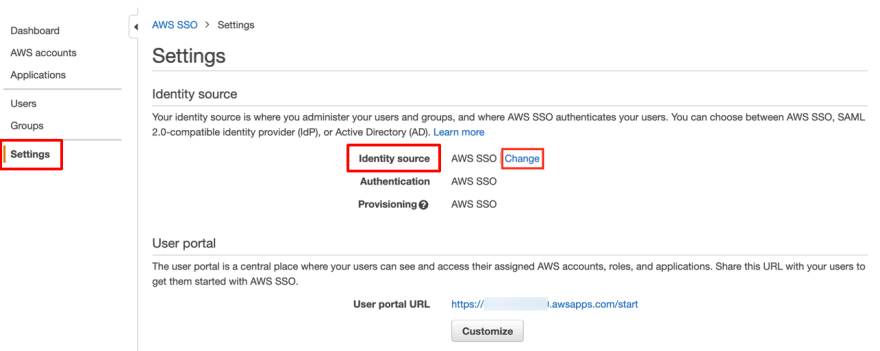
- Select the
Settings, from theIdentity sourceselectChange
- By default, AWS SSO uses its own directory (AWS SSO) as the identity provider. To use Google Workspace (G Suite) as your identity provider, you have to switch to an
external identity provider. SelectExternal identity providerfrom the available identity sources.
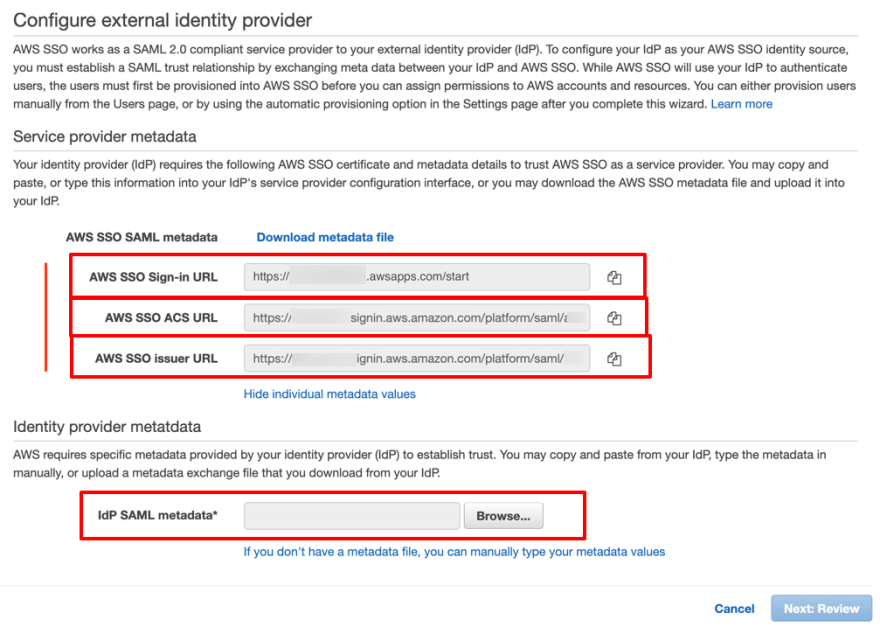
- Choosing the
External identity provideroption reveals additional information needed to configure it. ChooseShow individual metadata valuesto show the information you need to configure a custom SAML application.
Note down the AWS SSO SAML metadata information to configure the a custom SAML application in Google Workspace (G Suite)
For the next steps, you need to switch to your Google Admin
console and use the service provider metadata information to configure AWS SSO as a custom SAML application.
Now one a new tab and follow the bellow step for IdP SAML metadata* to complete the SSO setup.
Google Workspace (G Suite) SAML application setup
- Open your Google Admin console in a new browser tab, navigate to the
Web and mobile appssection, selectAdd App, and then selectAdd custom SAML app.
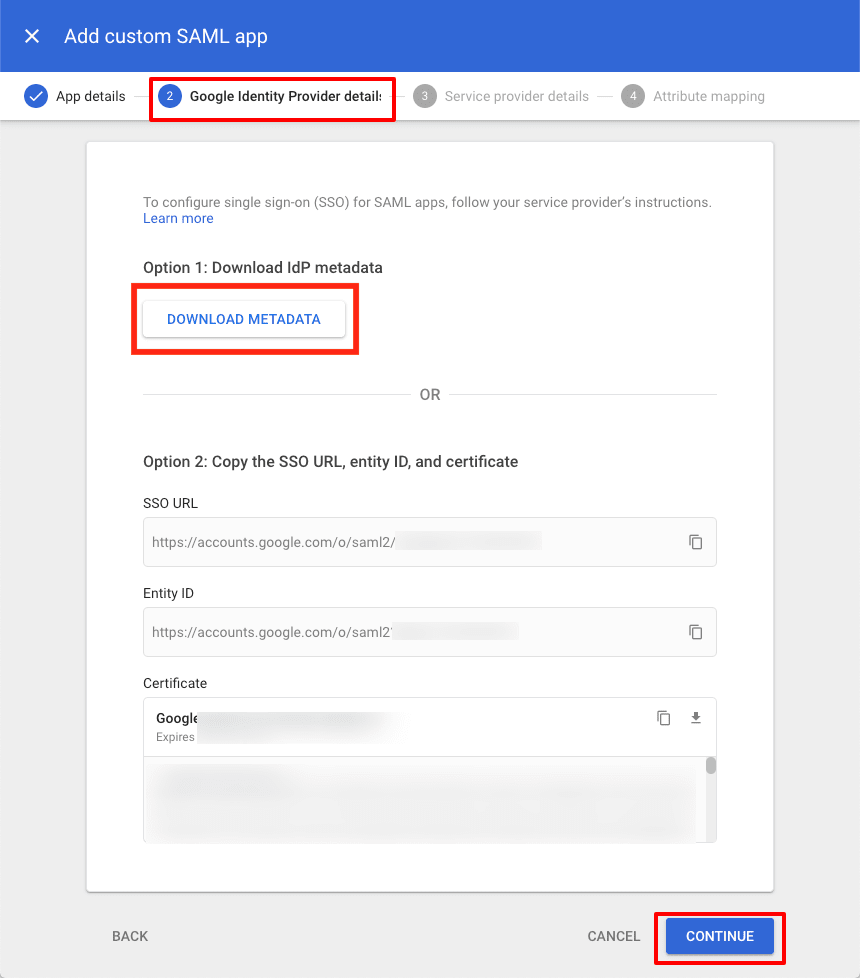
To configure the name of the application, in the
App detailssection, underApp name, enterAWS SSO(or any other name you want), and then chooseCONTINUE.To download the
Google IdP metadata, underOption 1: Download IdP metadata, chooseDOWNLOAD METADATA, and then chooseCONTINUE. This will downloads anXML filenamedGoogleIDPMetadata.xml, which you will use to configure Google Workspace (G Suite) as the IdP in AWS SSO.
- Using the data from AWS SSO you noted, provide information in the
Service provider details, and then chooseCONTINUE.
The mapping for the data is as follows:
- For
ACS URL, enter theAWS SSO ACS URL. - For
Entity ID, enter theAWS SSO Issue URL. - For
Start URL, leave the field blank. - For
Name ID format, chooseEMAIL. - For
Name ID, chooseBasic Information > Primary email.
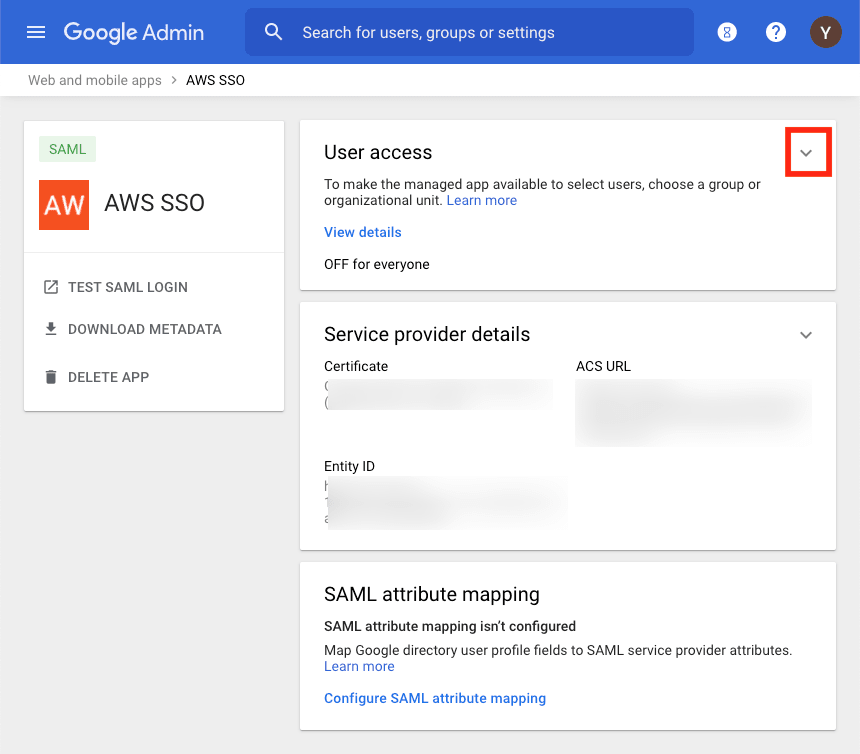
On the
Attribute mappingscreen, leave the default settings and chooseFINISH.On the application page, in the
User accesssection, select the down arrow to expand the section.
- select
ON for everyoneand chooseSAVE.
Congratulations! You have now enabled the application for all your users. But this doesn’t give access to any resources inside of your AWS accounts. Permissions are granted in AWS SSO.
Note: If you want to manage access for particular users you can do this via organizational units (for example, you can enable the AWS SSO application for your engineering department).
You’re done configuring AWS SSO in Google Workspace (G Suite). Return to the other browser tab with the AWS SSO configuration and complete the SSO setup.
Add identity provider metadata in AWS SSO
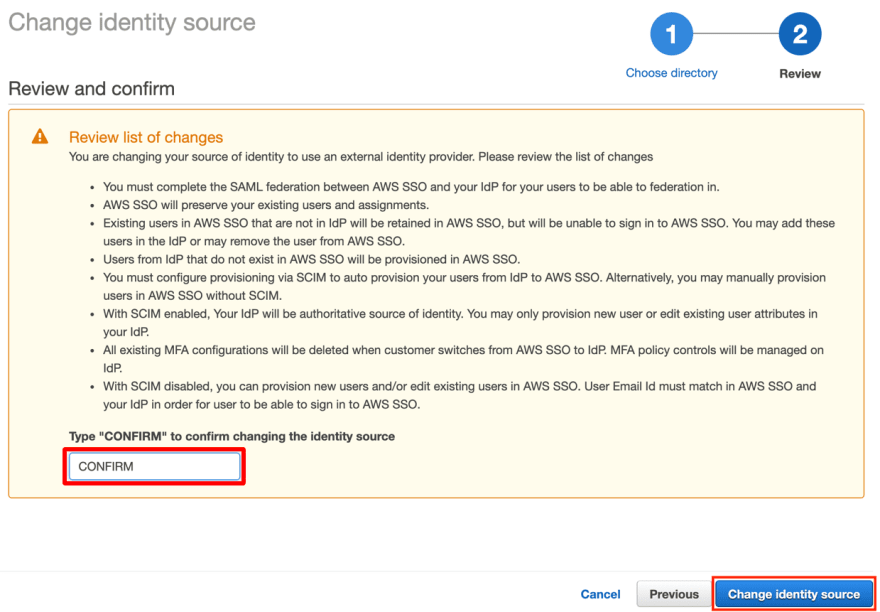
- SO you have done the Google Workspace (G Suite) setup and you downloaded the
GoogleIDPMetadata.xmlfile. ChooseBrowse…on the configuration page and select this file from your computer and clickNext: Reviewbutton.
- Type
CONFIRMand clickChange identity sourceto complete the setup.
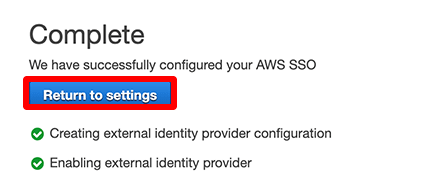
- Your configuration is completed! Now click
Return to settings
Add a user to AWS SSO
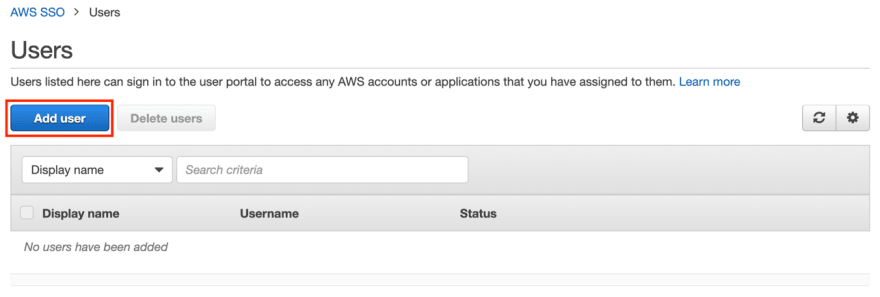
- Select
Usersfrom the sidebar of the AWS SSO overview page and then chooseAdd user.
- Enter the user details and use your user’s primary email address (username@gsuite_domain.com) as the username. Choose
Next: Groupsto add the user to a group.
- Skip the
Add user to groupsstep or you can select your's group(s) then clickAdd user.
You have successfully created a user!
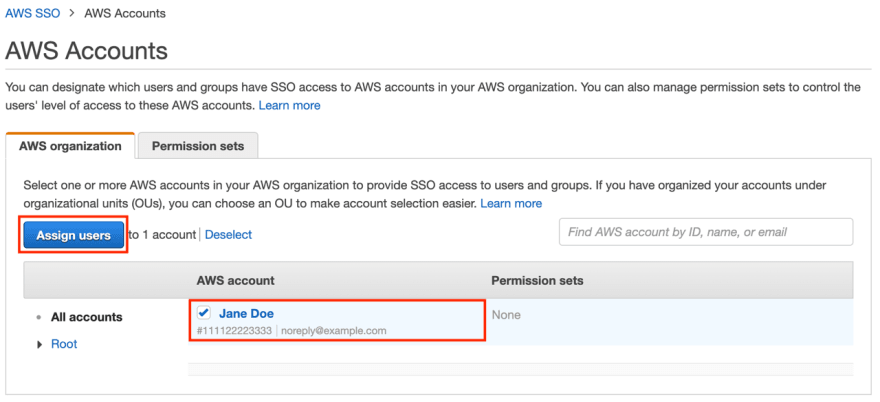
- Now assign the user to an AWS account in your AWS Organization. This allows the user to access the assigned account. Select the account you want to assign your user to and choose
Assign users.
- Select the user you just added, then choose
Next: Permission setsto continue configuring the effective permissions of the user in the assigned account.
- Since you didn’t configure a permission set before, you need to configure one now. Choose
Create new permission set.
- AWS SSO has managed permission sets that are similar to the AWS managed policies you already know. Make sure that
Use an existing job function policyis selected, then selectPowerUserAccessfrom the list of existing job function policies and chooseCreate.
- You can now select the created permission set from the list of available sets for the user. Select the
PowerUserAccesspermission set and chooseFinishto assign the user to the account.
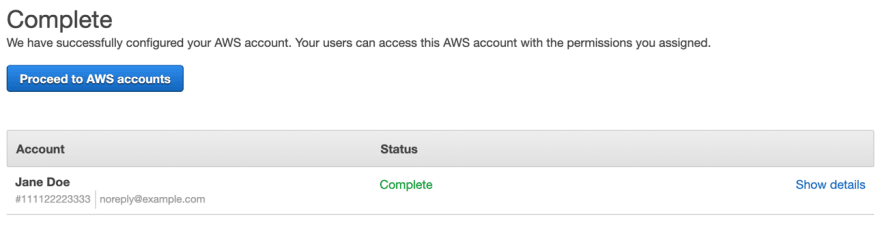
- You see a message that the assignment has been successful.
Access an AWS Account with Google Workspace (G Suite)
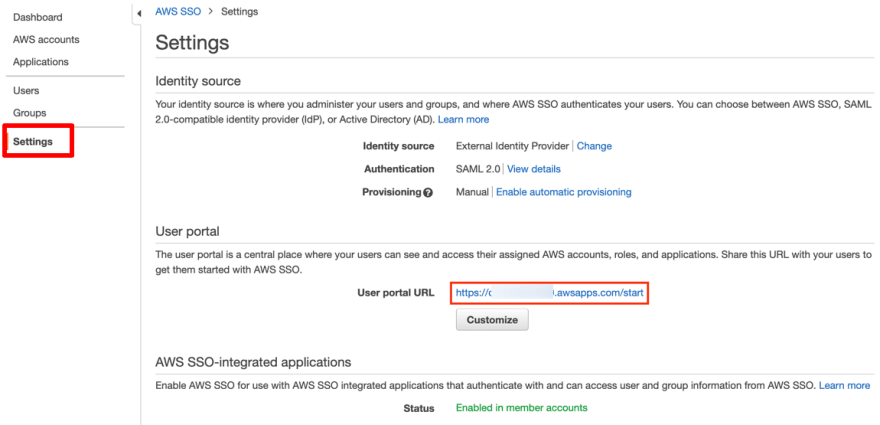
You can find your user portal URL in the AWS SSO settings, as shown in the following screenshot. Unauthenticated users who use the link will be redirected to the Google account login page and use their Google Workspace (G Suite) credentials to log in.
After authenticating, users are redirected to the user portal. They can select from the list of assigned accounts, as shown in the following example, and access the AWS Management Console of these accounts.
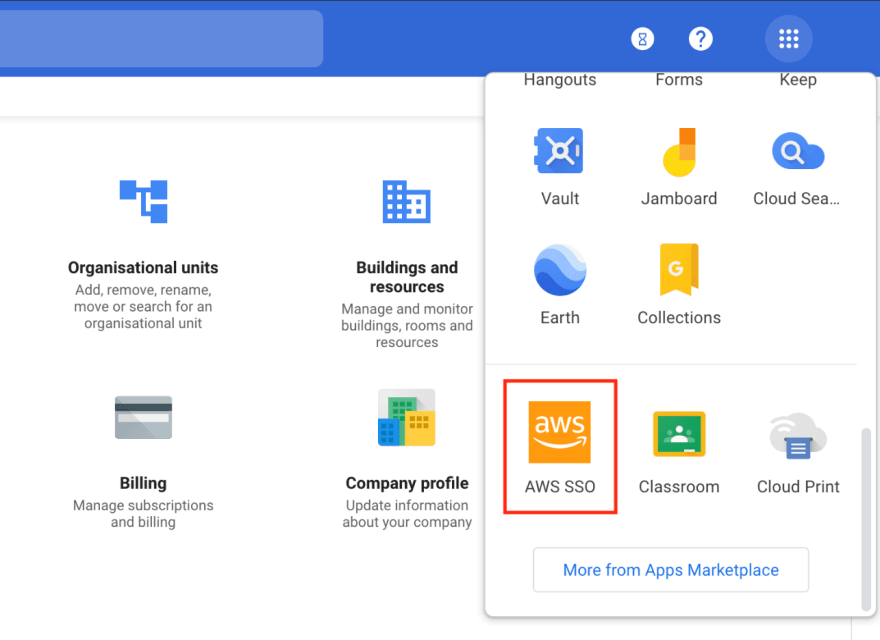
Another way your users can use AWS SSO is by selecting it from their Google Apps to be redirected to the user portal, as shown in the following screenshot. That is one of the quickest ways for users to access accounts.
You’ve successfully set up G Suite as an external identity provider for AWS SSO. Your users can access your AWS accounts using the credentials they already use.
Using AWS CLI with SSO
You can use the AWS Command Line Interface (CLI) to access AWS resources. AWS CLI version 2 supports access via AWS SSO. You can automatically or manually configure a profile for the CLI to access resources in your AWS accounts. To authenticate your user, it opens the user portal in your default browser. If you aren’t authenticated, you’re redirected to the G Suite login page. After a successful login, you can select the AWS account you want to access from the terminal.
To upgrade to AWS CLI version 2, follow the instructions in the AWS CLI user guide.
Summary
You’ve set up Google Workspace (G Suite) as an external IdP for AWS SSO, granted access to an AWS account for a G Suite user, and enforced fine-grained permission controls for this user. This enables your business to have easy access to the AWS Cloud.
Thanks for reading! Happy Cloud Computing!
Connect with me: Linkedin